SaaS Security Audit Checklist: Best Practices and Principles
SaaS tools (automated data storage and processing systems, management, etc.) are used today by almost any organization or enterprise. In this regard, ensuring the safety of information circulating in them becomes necessary. We had already touched on this topic before in development cost growth on a post-MVP phase of a SaaS product.
An audit is required to assess whether everything is in order with data protection and other aspects of information security. It allows you to obtain objective qualitative and quantitative assessments of the security indicators of information and other systems.
Let's figure out why conducting an information security audit is necessary, who it is better to entrust, what to look for, etc. It will help you protect yourself from the negative consequences of losing important data and eliminate legal problems (after all, relevant regulatory legal acts regulate information security).
What is SaaS Audit and Why It’s Important?
It is customary to call information security the protection of data from the interference of an accidental or intentional type, both artificial and natural, which can lead to financial or moral damage to the data owner. As a rule, the need to audit information security systems arises if the company's field of activity involves working with customers' personal data or financial information. An audit is the most effective way to obtain objective and real data on the condition.
As a result of a comprehensive SaaS development audit program within the framework established by the customer, the audit allows you to achieve several goals:
- Providing the customer with complete data on possible methods of penetration into the information system and the level of risk in various protection options;
- Planning different measures to reduce the level of risks - depending on the time span - urgent, medium-term, and long-term;
- Determination of the main directions for improving the information security system depending on the scope of the company;
- Drawing up plans for obtaining international certificates in the field of information systems security;
- Drawing up a reasonable financial plan for spending on information security and rationalizing costs;
- Consulting activities with specialists in the information security department of the customer's company, as well as the development of methodological manuals for ordinary employees.
We advise performing a security audit of information systems at least once yearly. Conducting audits more frequently is recommended in case of frequent changes in the company's structure, the scope of activity, or new security requirements. This proactive approach enables the timely adoption of appropriate methods, making management decisions and minimizing potential risks of data system breaches.
Types of Security Audit For SaaS Products
For ease of reference, it is customary to divide audit operations into several types - active audit (internal and external) and expert. Each of them is used depending on the situation and implies an assessment of protection systems in terms of programs' response to intrusions and comparison with generally accepted standards.
The process of assessing information security systems is a documented examination, the main task of which is to analyze a particular enterprise's data protection level. With objective data on the real state of security, developing an effective protection system will be possible. The entire audit procedure consists of several sequential operations:
- Setting the time and other frames of the proposed analysis, including the list of analyzed resources and other customary conditions;
- A comprehensive analysis of the protective systems of the customer's company within a clearly established framework, during which a survey of employees is carried out, a study of a technical and management package of documents in this area, testing of data system components;
- Analysis of the data that was obtained at the previous stages, which makes it possible to diagnose possible risks and make sure that the information security system complies with international requirements;
- Drawing up a list of measures to improve the quality of protection may include options for possible technical and organizational solutions, examples of estimates for implementing protection methods and methods of certification preparation based on international standards.
Internal Auditors
For smaller companies, the role of an internal auditor may be filled by a senior-level IT manager within the organization. This employee is responsible for building robust audit reports for C-suite executives and external security compliance officers. Larger companies tend to take this one step further, hiring designated Corporate Internal Auditors. These individuals usually have an impressive background as Certified Information Systems Auditors, Certified Internet Audit Professionals, or certified accountants.

External Auditors
An external auditor takes many forms, depending on the company's nature and the purpose of the audit. Some external auditors may be associated with federal or state government agencies, such as the Health and Human Services Office for Civil Rights. Others may work for third-party auditing firms that specialize in technology auditing. These auditors are hired when specific compliance frameworks, like SOX compliance, require it.
Now that we know who can conduct an audit and for what purpose, let’s look at the two main types of audits:
Manual Audits
An internal or external auditor can perform a manual audit. During this audit, the auditor will interview your employees, conduct security and vulnerability scans, evaluate physical access to systems, and analyze your application and operating system access controls.
Automated Audits
An automated audit is a computer-assisted technique known as a CAAT. These audits are run by robust software and produce comprehensive, customizable audit reports suitable for internal executives and external auditors. Advanced auditing software will even provide an extra layer of security, continuously monitoring the IT infrastructure and alerting IT technicians when suspicious activity occurs and when predetermined security thresholds have been crossed.
Cost of Audit For SaaS Product
From a single Google search, you can find anywhere from $1500 to $50,000 quoted for a security audit. So it depends. $1500 is a daily rate for an auditor, so a month of their time would cost around $30,000. In addition to the existing costs, utilizing penetration tests and other related services would incur additional expenses. You might want to use pen-testers in your portfolio audits and maybe your tollgates. So it depends.
Audits are essential to your overall security strategy in today's “we are all hacked” business climate. When looking for the security audit, we chose to work with CYLINX. They show your SaaS project is at risk and monitor your sensitive data for attacks from inside and out.
Best Practices for SaaS Security Audit: Full Guide
Regardless of which type of audit is chosen for a particular case, the following stages are distinguished on how to audit SaaS product properly:
Penetration Testing
Most often, the security check of a resource is carried out according to the "black box" method - a security specialist begins attempts to hack his target as if he were a real attacker and pursued some selfish goal:
- Hack a competitor.
- Attack site visitors.
- Secretly monetize the site from the owner or amuse your ambition.
Thus, a tester must solve at least one of the global problems:
- Violate the confidentiality of customer information.
- Restrict access to critical data.
- Modify or destroy any information without the possibility of its recovery.
As you can see from this list, you can't just take and audit the site. You need some preparation for penetration testing, without which it will either be ineffective or can become a real hacker attack with dire consequences. It would help if you did at least the following:
- Sign a non-disclosure agreement. Researchers can gain access to precious confidential information during their work. Reputable organizations involved in security testing are unlikely to use it for their purposes. Still, it is only sometimes possible to check the integrity of the performer, so it is better to conclude an agreement.
- Conducting an audit on a full copy of the main software data. The tester will use all methods of hackers, including those leading to a breakdown of a web resource or the destruction of data on it. It is better not to expose the combat version of the project to such stress and limit yourself to a clone.
- Concealment of the audit. The fewer people know about testing, the better. Attackers rarely warn about their attack, so if you tell many people about the event, this can distort the result.
Open Source Search
Since the "black box" method is used, the tester is absolutely not aware of what the attacked object looks like from the inside. Otherwise, hacking would be an extremely trivial task. Therefore, a preliminary collection of information is used.
A specialist is primarily interested in the technical side of a web application - in what language it is written, what CMS it uses, and with what extensions. You can find out all this without even resorting to special tools. Sometimes, only Google is enough. For example, you can find employees of the attacked company on LinkedIn, identify programmers among them, and determine what language they specialize in.
Moreover, you can find out what they were doing if you wish. To do this, search by their names or nicknames, and you can find many exciting things in the search results. It can be, for example, a discussion on behalf of this programmer of a module for the engine or an order from a corporate account with a freelance contractor of a new plug-in with detailed technical specifications.
Definition of Protective Equipment
The presence of some security software - intrusion prevention systems, DDoS protection, and firewalls - can seriously complicate the hacking task, so it must be detected. Usually, special programs are used for this. For example, you can detect the presence of a firewall using a port scanner, and domain DNS records determine anti-DDoS services.
Exploiting Common Vulnerabilities
Before looking for unknown zero-day vulnerabilities and examining the web application's logic and architecture, the tester will check the site's resistance to standard attack methods. For example, it may use a known exploit for an old engine version. At this stage, the aforementioned Interpark and the Ubuntu forum suffered.
In general, at this stage, the following usually happens:
- An attempt was made to execute code remotely.
- Attempted SQL injection.
- The exploitation of XSS, RFI, and LFI vulnerabilities.
- Search for backup storage locations and gain access to them.
- Manipulations with the authorization system: brute force, search for unsafe password recovery, bypass authentication.
- Studying the site's file structure to find files, access to which is limited only by the absence of a direct link to it.
- Traffic interception and research.
- Search for options for unauthorized access to confidential information.
An Unconventional Approach
When well-known methods do not help, the tester, combining all the practices described above and his understanding of security systems, tries to bypass the existing protection or discover a hitherto unknown vulnerability.
Not all auditors carry out this procedure since it is pretty complex, requires very high qualifications of specialists, and costs a lot. As practice shows, sometimes zero-day vulnerabilities are discovered by third-party researchers; however, they receive a corresponding reward for finding them.
In fact, if your site is successfully tested for all standard types of threats, then the test can be considered successful. A more detailed and in-depth study of hacking methods is relevant only for huge projects, for hacking can involve high-class hackers who can discover new security holes.
Completion of the Audit
The result of any penetration testing is a document that must include:- Information on the methods used at the time of the inspection.
- Development of an attacker's concept, potential goals, and motivation.
- Description of attack scenarios developed and implemented by testers.
- A detailed report on all vulnerabilities found.
- Recommendations for their elimination.
Our Experience in SaaS Security Auditing
We have already mentioned our brainchild called Stripo-email template builder many times. This SaaS product was repeatedly hacked at the initial stage. And we even got several emails from Indian hackers, who found some vulnerabilities in our system and asked for money for a hint to fix it and for the fact that they would not try to hack us.
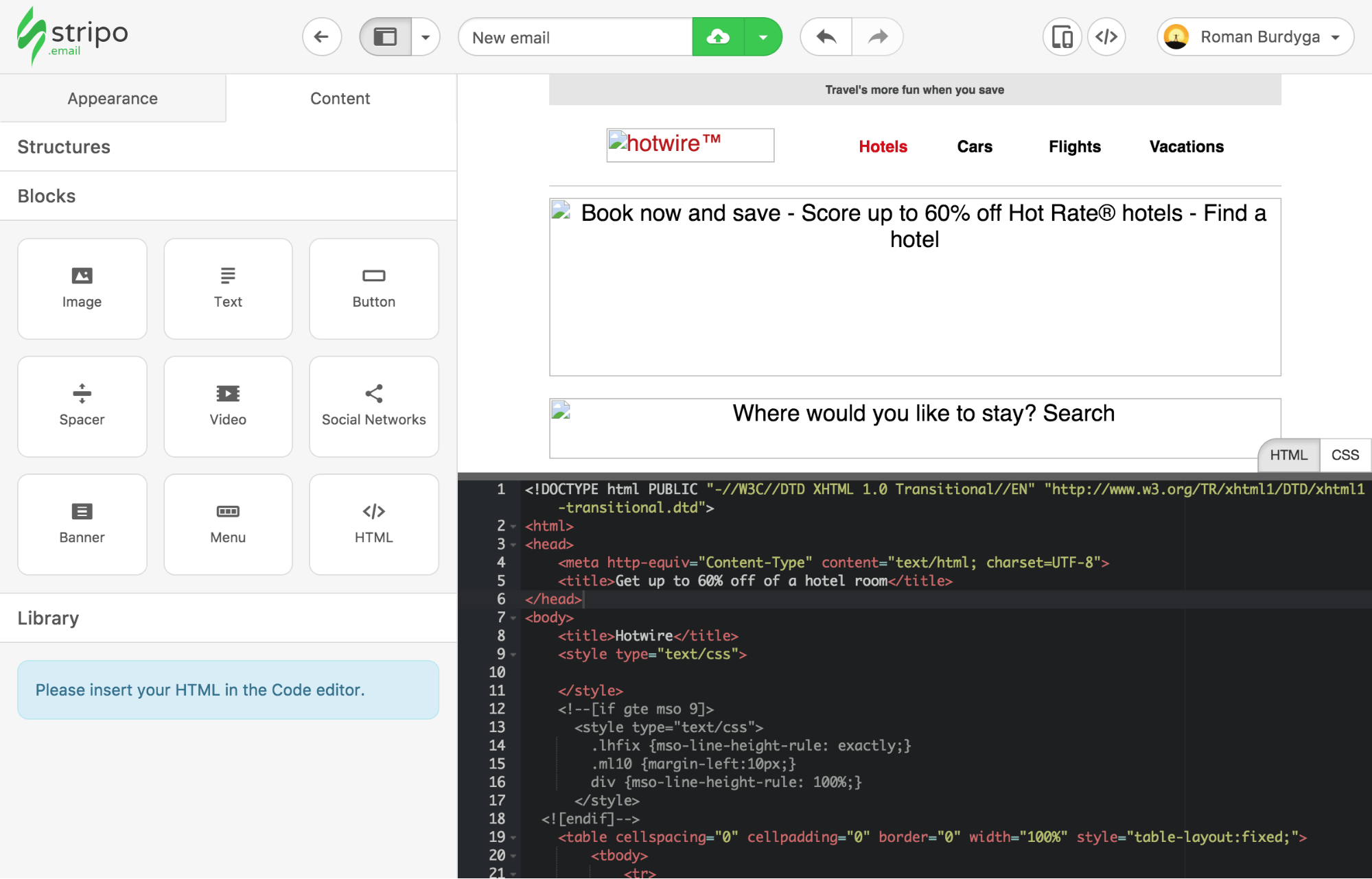
There were cases when clients from Russia wrote scripts and created 1,500 fake accounts to receive 5 test emails for free. However, now the meaning of such cheating has exhausted itself since we have changed the terms of use and now you can send an email for free only to yourself.
Another way to seduce hackers was using the public API, but over time, we closed it and allowed it to be used only after verification.
The audit SaaS provider, with which we cooperate in security audit, is a certified Google partner, which was very important to us. Every year, they conduct a certification audit process for SaaS project, such as the reliability of the Stripo in a variety of ways, including:
- Penetration testing;
- Hacking an application;
- Putting the system down;
Typically, they send a 60-page report for correction after such an audit. Also, we receive about 10-15 notifications of hacking attempts every month.
Ensure the Security of Your SaaS Applications with Ardas
A competently performed audit effectively finds weaknesses in the SaaS and its server. The test is rarely passed completely, and the developers usually need to pay more attention to some details. But even if the web resource could not be hacked, this is still a result - now its owner will be able to sleep peacefully.
Working on many projects from the beginning, our dedicated development team is used to taking into account what security measures need to be followed to minimize future attempts to hack your project. Therefore, if you still have questions or want to entrust us with the safe custom development of your idea, Ardas is ready to help you!