


We Help You To
Our SaaS Development Services
We bring together a cross-functional team to cover every stage of modern SaaS development — from re-architecture to scaling, AI feature delivery, and long-term platform growth. Whether you're modernizing legacy code, optimizing for performance, or embedding AI, we tailor solutions to your tech and product goals.
Our SaaS Software Development Process

Technologies We Use for SaaS Development
Backend
Frontend
Mobile
Data Science & BI
Cloud & DevOps
Databases & Storage
AI & Machine Learning
Why choose Ardas
Transparency
We ensure complete transparency throughout our SaaS app development process thanks to regular updates and open communication channels
SaaS Expertise
We’ve developed 3 own SaaS and more than 70 clients’ SaaS products, so we know exactly how to make your startup a unicorn
Estimation Accuracy
The same team that is assessing your project will work on the project that our estimates hit with 90% accuracy
Experts in Processes
Having worked on projects of all sizes, we've spent 20 years refining our SDLC processes through hands-on experience
Budget in Control
No unplanned expenditure. We report on the time spent and plan the development of all subsequent stages
Fast Scaling
We eliminate everything that doesn’t add value to a product and cut the delivery cycle to win time for improvements
Team Engagement Models for SaaS
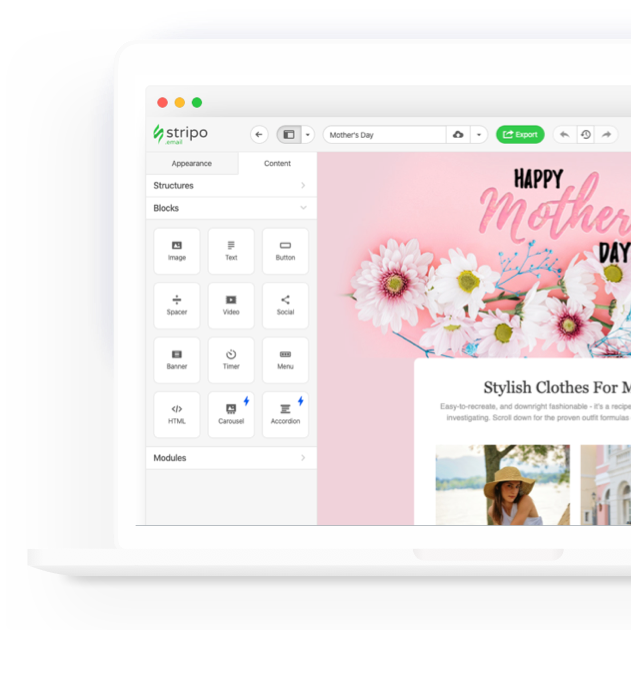
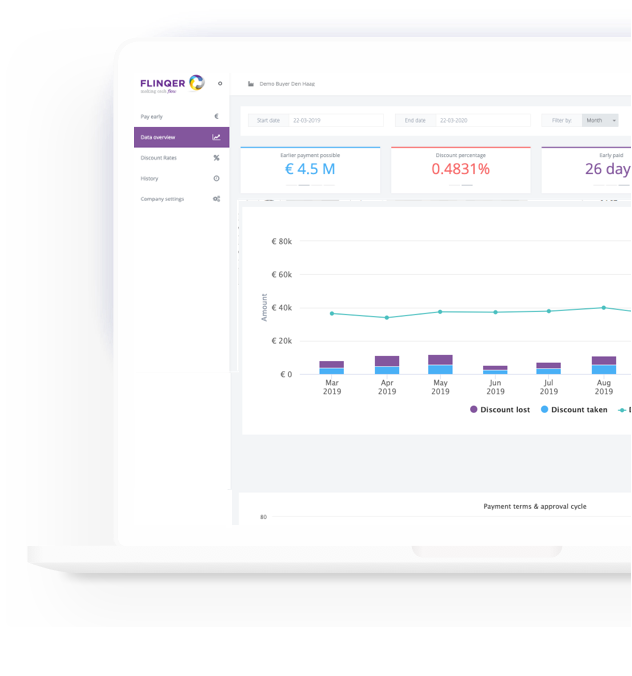
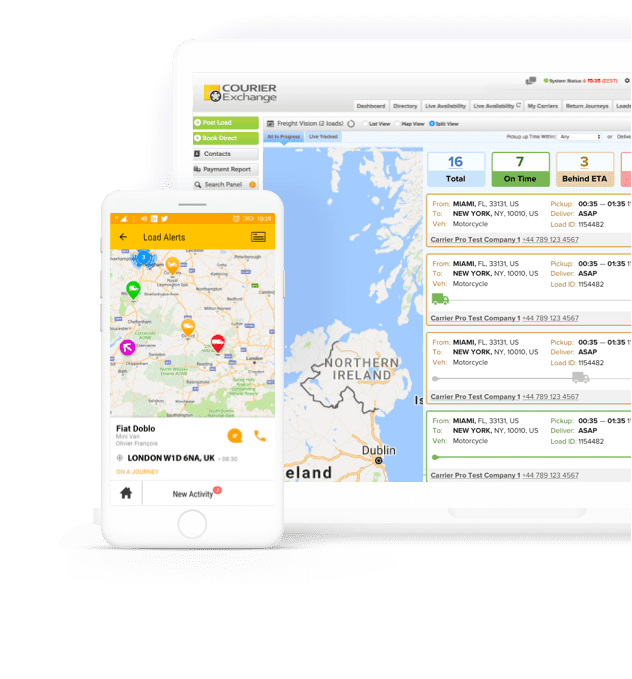
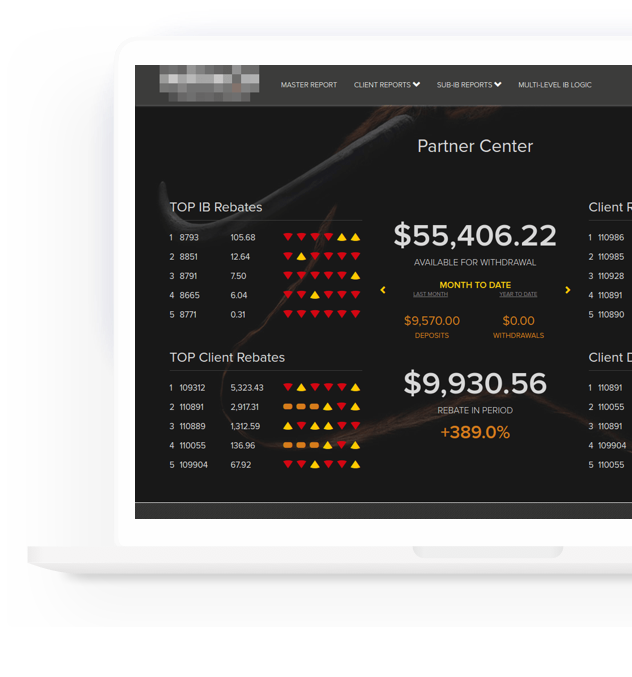
SaaS Success Stories
Clients Say About Us
Why working with us is low-risk and enterprise-ready?
We worked hard to create a safe and confident SaaS development services and support processes
Work for hire
IP for all software is 100% yours
ISO 9001 certified
Well-polished management and processes
ISO 27001 certified
The highest attention to security
NDA and DPA agreement
We take responsibility for nondisclosure of important business matters and privacy of your customers' data
Fully insured business
Even if something goes wrong from our side, you do not risk your money. Our company is insured to protect your invested money in project
Recognitions
and Partnerships
What We Can Do As SaaS Developers
FAQ
Why Should You Choose Custom SaaS Applications?
Choosing a custom SaaS development enables businesses to gain access to applications over the Internet and eliminates the need for costly and complex software and hardware management. Custom SaaS applications allow businesses to scale, backup and recover their data from the cloud and increase their security.
How Much Does it Cost to Develop a SaaS?
SaaS application development services usually start from $30K. Nevertheless, by making well-informed decisions, you can save considerable amounts and enhance the overall system’s utility, quality, performance, safety, and eventually, its profitability on the market. Whether you wish to convert your original software into SaaS or to start a SaaS business from scratch, Ardas can help with every stage of SaaS application development.
How to Build a SaaS Product?
There is a step-by-step process to launch a SaaS product. First, fill out the form below and let us contact you. Then our team will find out your needs and study the market. As soon as it is done, we will provide a SaaS development plan, gather the dedicated team and get to building an MVP. After this stage is done, we are only left to build the rest, launch and support.
What does a successful AI transformation look like for SaaS companies?
Successful AI transformation means more than just adding AI features—it requires a clear strategy, quality data, cross-functional collaboration, and iterative model development. It involves integrating AI to solve real user problems, continuously measuring impact, and evolving capabilities as your product and customers grow.
How can AI be integrated effectively into SaaS products?
Effective AI integration requires aligning AI features with real user needs, ensuring clean and well-structured data, and embedding AI models into your product’s workflows. It also involves continuous monitoring, model retraining, and balancing automation with human oversight to maximize value.
What is Multi-Tenant SaaS?
Multi-tenancy means that a single instance of the software and its supporting infrastructure serves multiple customers. Each customer shares the software application and a single database, and each tenant’s data is isolated and remains invisible to other tenants. The benefits of multi-tenant are the affordable price, cloud environments allow for easier integration with other applications and “hands-free” maintenance.
What is SaaS Architecture?
SaaS architecture refers to a specific kind of IT setup for Storage as a Service. SaaS architecture is about how Software as a Service programs are deployed and set up within a business IT structure. Another related term is Service Oriented Architecture or SOA. It includes software as a service and other elements of a business software system. The idea is to streamline how all of the various software programs in business operations are set up.
Start Building Your SaaS the Right Way
No matter what stage your SaaS solution is at, reach out for a free consultation. We respond quickly and help you onboard engineers with proven SaaS expertise, align your priorities, and deliver realistic project estimates.